Digital&computforensic
- 1. Digital & Computer Forensic 1 By :Rahul Badekar (2) ME(IT)
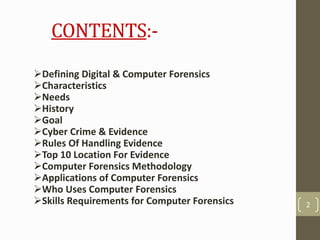
- 2. CONTENTS:- Defining Digital & Computer Forensics Characteristics Needs History Goal Cyber Crime & Evidence Rules Of Handling Evidence Top 10 Location For Evidence Computer Forensics Methodology Applications of Computer Forensics Who Uses Computer Forensics Skills Requirements for Computer Forensics 2
- 3. What is Digital Forensics? • “Digital forensics (sometimes known as digital forensic science) is a branch of forensic science encompassing the recovery and investigation of material found in digital devices, often in relation to computer crime. • Digital forensics was originally used as a synonym for computer forensics but has expanded to cover investigation of all devices capable of storing digital data. • The technical aspect of an investigation is divided into several sub-branches, relating to the type of digital devices involved computer forensics, network forensics, forensic data analysis and mobile device forensics. 3
- 4. What is Digital Forensics? 4
- 6. 6 The Process • The primary activities of DFS are investigative in nature. • The investigative process encompasses • Identification • Preservation • Collection • Examination • Analysis • Presentation • Decision
- 8. 8 Subcategories of DFS • There is a consensus that there are at least 3 distinct types of DFS analysis • Media Analysis • Examining physical media for evidence • Code Analysis • Review of software for malicious signatures • Network Analysis • Scrutinize network traffic and logs to identify and locate
- 9. What is Computer Forensics? • “Forensic computing is the process of identifying, preserving, analyzing and presenting digital evidence in a manner that is legally acceptable.”(Rodney Mckemmish 1999). • Evidence might be required for a wide range of computer crimes and misuses. • Information collected assists in arrests, prosecution, termination of employment, and preventing future illegal activity 9
- 10. What is Computer Forensics? 10 Fundamentals Military Acquisition Analysis Examination Report Investigation Criminal FRYE FRE 702 Daubert/Kumho Civil Federal Rules of Civil Procedure Sedona Rowe Rules of Evidence Expert Witness Friend of the Court Technical Expert Presentation Standards & Guidelines Law Enforcement Private Sector Computer Forensics
- 11. Characteristics of Computer Forensic • IDENTIFYING • PRESERVING • ANALYZING • PRESENTING 11
- 12. Needs of Computer Forensic • To produce evidence in the court that can lead to the punishment of the actual. • To ensure the integrity of the computer system. • To focus on the response to hi-tech offenses, started to intertwine. 12
- 13. History of Computer Forensic • Began to evolve more than 30 years ago in US when law enforcement and military investigators started seeing criminals get technical. • Over the next decades, and up to today, the field has exploded. Law enforcement and the military continue to have a large presence in the information security and computer forensic field at the local, state and federal level. 13
- 14. Goal of Computer Forensic • The main goal of computer forensic experts is not only to find the criminal but also to find out the evidence and the presentation of the evidence in a manner that leads to legal action of the criminal. 14
- 15. Cyber Crime & Evidence • CYBER CRIME • Cyber crime occurs when information technology is used to commit or conceal an offence. 15
- 16. Types of Cyber Crime • Forgery • Breech of Computer Security • Fraud/Theft • Copyright Violations • Identity Theft • Threats • Burglary • Homicide • Administrative Investigations • Cyber Terrorism • Sales and Investment Fraud • Electronic Fund Transfer Fraud 16
- 17. 17
- 18. Cybercrime: Top 20 Countries 18
- 19. Evidence • An item does not become officially a piece of evidence until a court admits it. • Much of forensics practice concerns how to collect, preserve and analyze these items without compromising their potential to be admitted as evidence in a court of law. 19
- 20. Digital Evidence • “Any data that is recorded or preserved on any medium in or by a computer system or other similar device, that can be read or understand by a person or a computer system or other similar device. It includes a display, print out or other output of that data.” 20
- 21. Types of Digital Evidence 1) PERSISTANT DATA Meaning data that remains intact when the computer is turned off. E.g. hard drives, disk drives and removable storage devices (such as USB drives or flash drives). 2) VOLATILE DATA, Meaning data that would be lost if the computer is turned off. E.g. deleted files, computer history, the computer's registry, temporary files and web browsing history. 21
- 22. 5 Rules of Evidences 1) Admissible • Must be able to be used in court or elsewhere. 2) Authentic • Evidence relates to incident in relevant way. 3) Complete (no tunnel vision) • Exculpatory evidence for alternative suspects. 4) Reliable • No question about authenticity & veracity. 5) Believable • Clear, easy to understand, and believable by a jury. 22
- 23. TOP 10 Location For Evidence 1) Internet History Files 2) Temporary Internet Files 3) Slack/Unallocated Space 4) Buddy lists, personal chat room records, others saved areas 5) News groups/club lists/posting 6) Settings, folder structure, file names 7) File Storage Dates 8) Software/Hardware added 9) File Sharing ability 10) E-mails 23
- 24. Applications :- • FINANCIAL FRAUD DETECTION • CRIMINAL PROSECUTION • CIVIL LITIGATION • “CORPORATE SECURITY POLICY AND VIOLATIONS” 24
- 25. Who Uses Computer Forensics? • Criminal Prosecutors • Rely on evidence obtained from a computer to prosecute suspects and use as evidence. • Civil Litigations • Personal and business data discovered on a computer can be used in fraud, harassment, or discrimination cases. • Private Corporations • Obtained evidence from employee computers can be used as evidence in harassment, fraud, and embezzlement cases. 25
- 26. Who Uses Computer Forensics? (cont..) • Law Enforcement Officials • Rely on computer forensics to backup search warrants and post-seizure handling. • Individual/Private Citizens • Obtain the services of professional computer forensic specialists to support claims of harassment, abuse, or wrongful termination from employment. 26
- 27. Skills Required For Computer Forensics Application • Programming or computer-related experience • Broad understanding of operating systems and applications • Strong analytical skills • Strong computer science fundamentals • Strong system administrative skills • Knowledge of the latest intruder tools • Knowledge of cryptography and steganography • Strong understanding of the rules of evidence and evidence handling • Ability to be an expert witness in a court of law 27
- 28. ` 28